
Unlock a seamless digital front door with Cloud-based telephony
Discover why telephony remains vital for a connected digital front door and improves patient access, efficiency and practice sustainability.

Delivering the vision of a neighbourhood NHS in 2025
Discover how Surgery Assist supports the neighbourhood NHS vision by improving patient access, easing GP workload, and enabling a more preventative, community-focused approach to primary care.

Unlock Knowledge and Win Big with the Academy this Easter!
Whether you’re a beginner learning the basics or an experienced user seeking quick answers, the Academy provides everything you need at your fingertips. And now, with our CPD-accredited courses, expanding your knowledge has never been more valuable. For a limited time – you can even WIN prizes!

The Rise of Online Video GP Appointments in Primary Care
The healthcare landscape is rapidly evolving, and primary care is at the forefront of this transformation. Data has highlighted a significant increase in online video GP appointments, in this blog Head of Product, Melissa Lato explores how the Surgery Connect Phonebar can help.
It’s time to build confidence around AI in primary care
Discover how AI in primary care can help to provide increased capacity for practices and better manage patient demand.
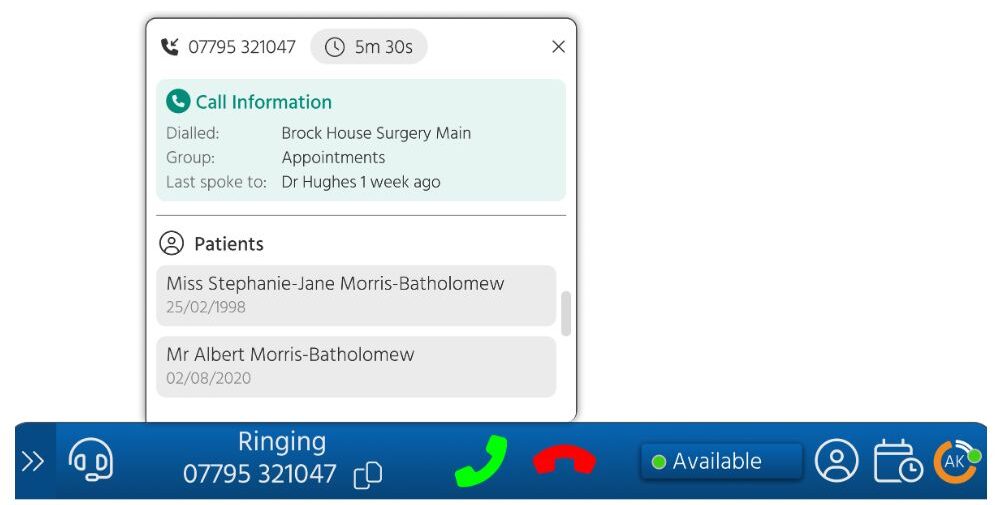
How Surgery Connect’s Phonebar Improves Patient Access and Boosts Efficiency in GP Practices
In today’s fast-paced primary care environment, having a robust communication system is no longer a luxury—it’s a necessity. That’s where Surgery Connect comes in, a digital telephony solution specifically designed for GP practices. In this blog, Joanne Dodd, Regional Sales Manager dives into the many reasons to adopt the Phonebar and utilise the softphone!
How to Enhance Patient Experience with Patient Callback
In the evolving landscape of primary care, delivering an exceptional patient experience is more critical than ever for modern general practice success. It’s not just about having the right tools in place; healthcare providers must know how to utilise these tools effectively to optimise patient interactions and streamline operations.
One such tool that can make a real difference is the Patient Callback feature. In this blog, Krista Read, Regional Sales Manager explores how.
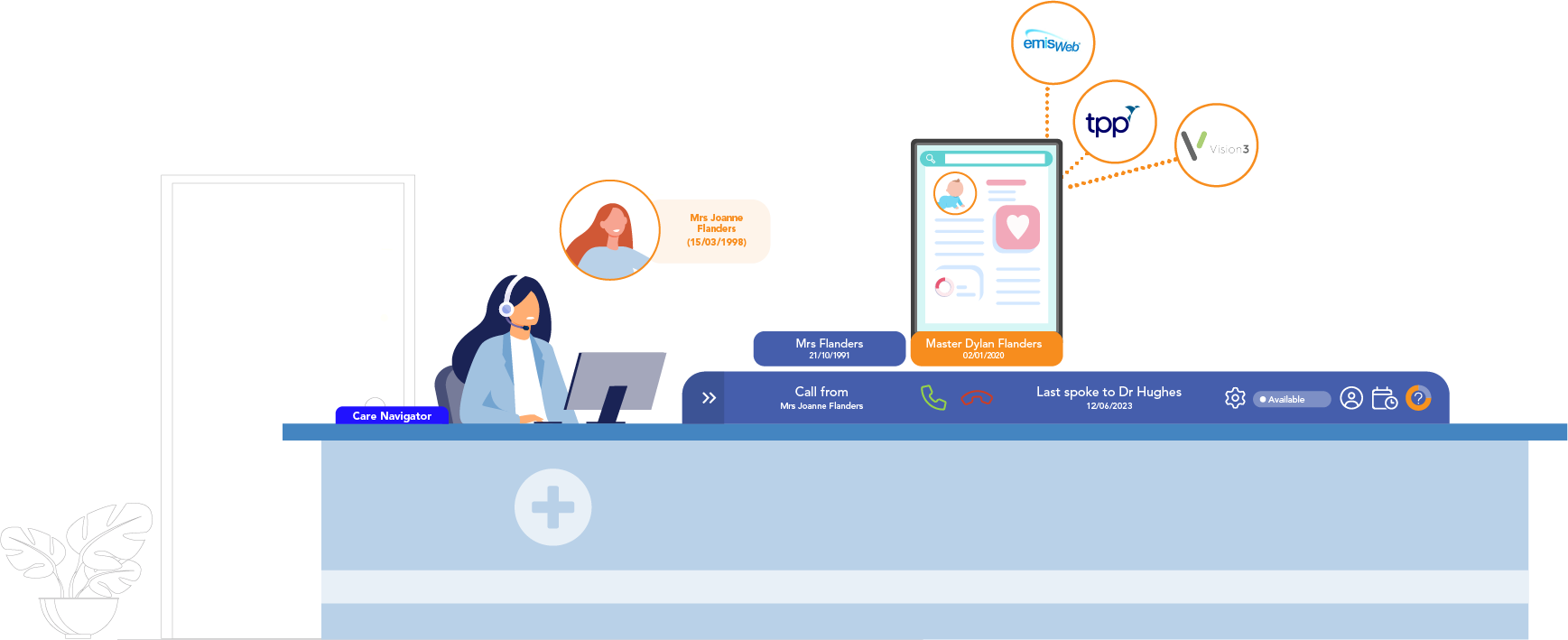
Why enhancing efficiency with Clinical System Integration impacts patient experience
In this blog, we explore how Clinical System Integration with Surgery Connect can optimise patient communication and administrative efficiency within your practice. Learn how it reduces costs, enhances data quality, and improves compliance, all while empowering patients. Uncover the key benefits and advanced features that will improve patient access and streamline some of the operations at your practice.
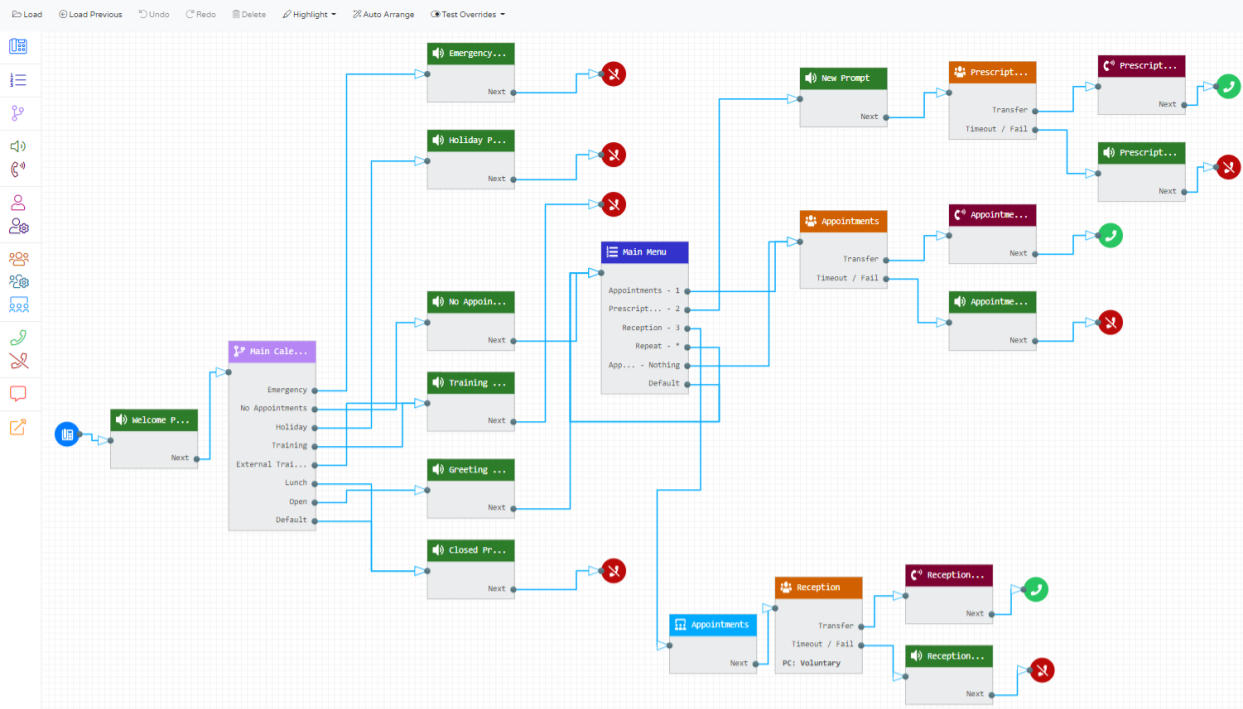
How Call Routing can help to deliver exceptional patient experience in Modern General Practice
We believe that Call Routing is crucial to enhancing your patients’ experience, ensuring swift access to other services (where appropriate) by seamlessly redirecting to alternative pathways, such as the NHS App or Pharmacies, whilst optimising staff efficiency. In this blog, Danielle Henderson describes why.
